This essay was written by lower-sixth former Ishan Nathan, and shortlisted for the 2020 Fifth Form Transitional Research Project. The following provides a short abstract to the full essay, which can be found at the bottom.
Estimated read time of abstract: 2 minutes
Estimated read time of essay: 15 minutes
The academic study of prime numbers has been of mathematical interest for centuries and over time remarkable progress has been made in understanding the unique properties and patterns of these numbers. Over the last fifty years, the discovery of mathematical models has aided the progression of computer science. Whilst encryption, previously used for communication in the wars, has now been adopted into quotidian life. Mathematicians have discovered new methods for the secure transmission of information and have augmented them by introducing new messaging platforms using encryption algorithms based on prime numbers.
It is widely accepted that Prime numbers are important in the field of number theory as they act as the “atoms of arithmetic”. They are defined as natural numbers greater than one, that are only divisible by exactly two numbers, one and itself. Mathematicians first studied primes explicitly in 300BC in Ancient Greek Mathematics, where Euclid proved that there was an infinitude of primes. Since then the understanding of primes has developed and the characteristics of primes enable it to have profound applications in security codes, blockchain analysis, cicada’s cycles, and Cryptography. Nevertheless, mathematicians do not understand the primes fully, due to their enigmatic behaviour whereby they appear to act randomly despite having some aspects of their behaviour which are predictable.
Prime numbers and their application to modern-day life is not always apparent, as is their properties and patterns. Yet prime numbers play a fundamental part in our lives and act as a cornerstone for both: day to day messaging on encrypted platforms such as WhatsApp, and for consumers’ online e-commerce activities. The emergence of the internet has led to an increase in the number of online transactions taking place all over the internet on sites like eBay and Amazon, and modern-day cryptographic methods establish a mechanism for a secure form of communication.
The RSA algorithm relies upon the quick speed for performing operations to determine large primes, and the computer-intensive reverse process in factorising large integers, in turn assuring the security of public-key cryptography. It is this high level of encryption that ensures the world of e-commerce to function protecting our sensitive information such as credit cards from the global market place. Yet what if there was a way to overcome this?
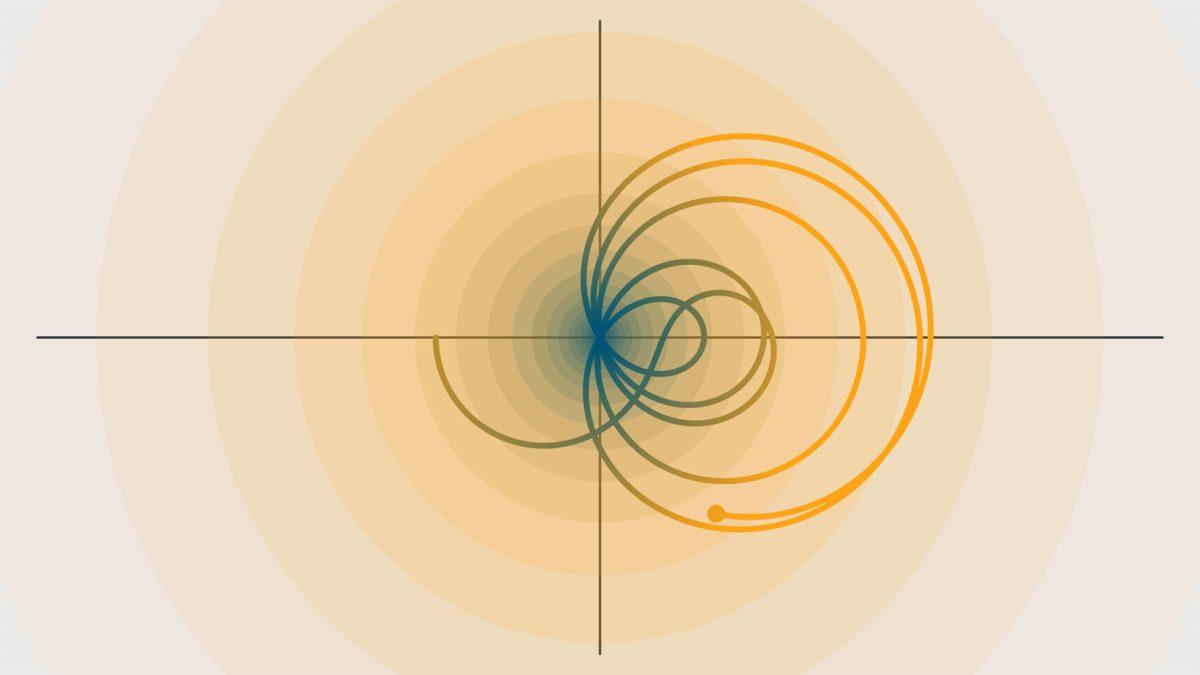
The Riemann Hypothesis is widely accepted as one of the biggest mathematical unproven conjectures of our millennium. It is argued that the Riemann Hypothesis predicts the distribution of the primes and their unpredictable behaviour better than any other theorem. An abstract proof of the Riemann Hypothesis will undoubtedly enhance our understanding of primes and thus could lead to vulnerabilities within asymmetric cryptography. However, primes are special and they are like no other group of numbers. Despite mathematicians limited understanding of these numbers, a secure online communication network across the world has been created; just imagine the possibilities that could unravel when understanding the true enigmatic behaviour of prime numbers.
To view Ishan’s full article, follow this link below.